In the past years, we have built numerous blockchain projects – most of them private permissioned networks with Proof of Authority (PoA: A defined number of nodes “control” the network). Every now and then, we encounter the question “Are private permissioned blockchain systems less safe?“. We sat down to clarify this question on a high level.
We won’t jump into technical details. Instead, let’s look at how a private permissioned blockchain network comes into existence: Someone gets the brilliant idea to create a shared network for a specific case in which data must be effectively shared between multiple parties. She might go to other parties and ask them to join her case and present them a beautiful Big Picture. Most likely, the others will react tentatively – they might have to turn larger wheels within their environment in order to join. So, our lone blockchain pioneer might collect loose commitments from those parties and have them intend to join (after the system has been created and proven, of course) and start out on her own.
Hence, the first step is taken to create a private permissioned blockchain network. And, as all first steps, it costs some effort and is in the beginning just – a step. A blockchain network with perhaps 2-3 nodes for a start. Very small, controlled by one entity and – admittedly – vulnerable. “Less safe”. In terms of security, there is no great difference here compared to a traditional centralized network with “a server”.
But, dear reader, we are forgetting something cruical: The Big Picture.
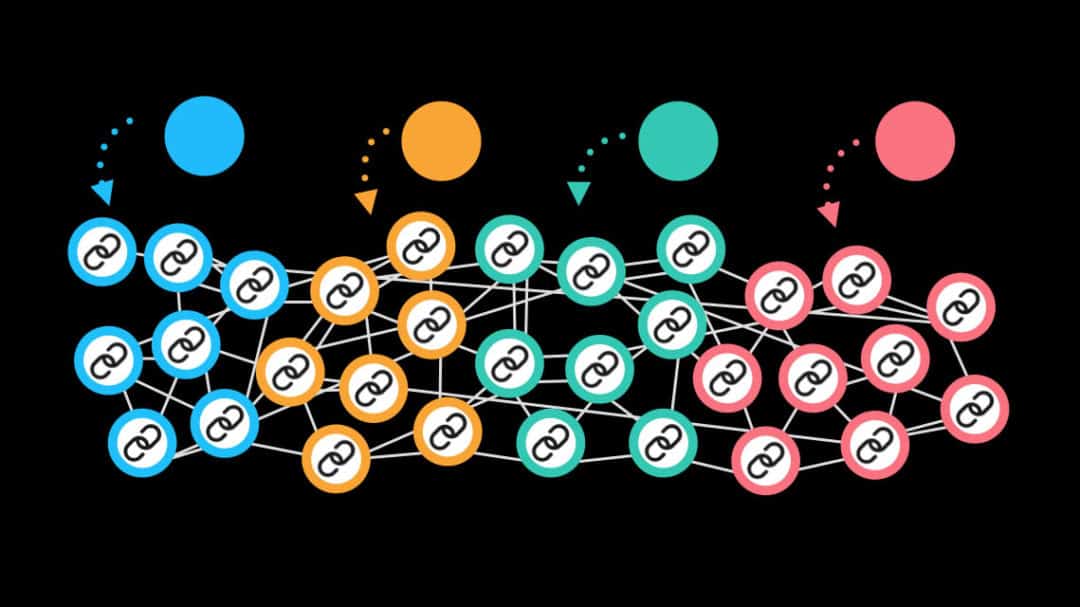
A seed does not make a forest, but it can start one. Our pioneer now will go to the parties she has collected commitments from. One or two will agree in testing. In an ideal case, they will see the benefit (usually it’s largely increased efficiency and/or cost savings) and better understand the Big Picture. With this lever, they will be able to turn the wheels in their environment – and add their own nodes to the network. With more parties joining the network over time, we have a consortium of real world entities which controls the network. They will create a governance model in order to set down the rules for the network. And of course, with the added nodes the network becomes safer.
So, on top of the technology (consensus algorithms, encryption, blocks, keys, distribution, zero knowledge proofs, channels… you name it) exists a real world layer to the network which is typically ignored by people who are fresh to the idea of private permissioned blockchains. This real world layer ideally contains
- a consortium (often found in form of a foundation),
- a governance model (set of rules agreed upon by the consortium)
- arbitration (to some extent automated within the network)
- auditing (possibly even through nodes of a neutral audit company for real-time auditing)
Can a large private permissioned blockchain network still be captured by a malicious party? Yes. BUT: This party will knowingly risk its reputation within the consortium, since it is transparent who holds which nodes. Imagine a humanitarian supply blockchain in which a number of humanitarian organizations make up the consortium. Would it make sense for one of these to risk their reputation? Imagine a money-transfer blockchain network held by a consortium of banks – would a bank want to risk its reputation? Or, think universities issuing degrees on a blockchain?
Are private permissioned blockchain systems less safe? It depends. Next time you encounter one, take a step back and challenge yourself: What could the big picture look like?
